Hear from Our Customers

You know the feeling. An employee leaves and you’re stuck wondering if they made copies. A key goes missing and suddenly you’re rekeying every door. Someone shows up after hours and you have no record of who or when.
Access control systems eliminate that uncertainty. You see who entered, when they came in, and which doors they accessed. You grant or revoke credentials from your phone in seconds, not hours spent rekeying locks.
When your building security runs on mobile credentials and cloud-based management, you’re not chasing down physical keys or wondering if yesterday’s terminated employee can still get in tonight. You control access in real time, from anywhere, with a complete audit trail of every entry.
We’ve been handling security for Delaware County businesses since the late 1800s. That’s four generations of locksmiths who’ve seen every lock problem, every security vulnerability, and every half-baked installation that needed fixing.
Tom McCausland and his daughter Chrissy run the largest locksmith operation in the Delaware Valley from our fully stocked Prospect Park storefront. We’re not a van with a phone number—we’re a real shop with real inventory and technicians who’ve been serving Concord businesses for decades.
In a community where the median household income tops $120,000 and business owners expect professional-grade security, you need installers who understand both the technology and the stakes. We handle everything from simple door entry systems to complex multi-building access control networks, with the same attention to detail that’s kept Delaware County businesses secure for over a century.

First, we walk your property. You show us which doors need control, who needs access, and what security concerns keep you up at night. We assess your current infrastructure, identify vulnerabilities, and recommend systems that actually fit your operation—not the most expensive option in the catalog.
Next, we design your access control system around how your business actually works. That means understanding employee schedules, delivery patterns, after-hours access needs, and integration with any existing security cameras or alarm systems you’re already running.
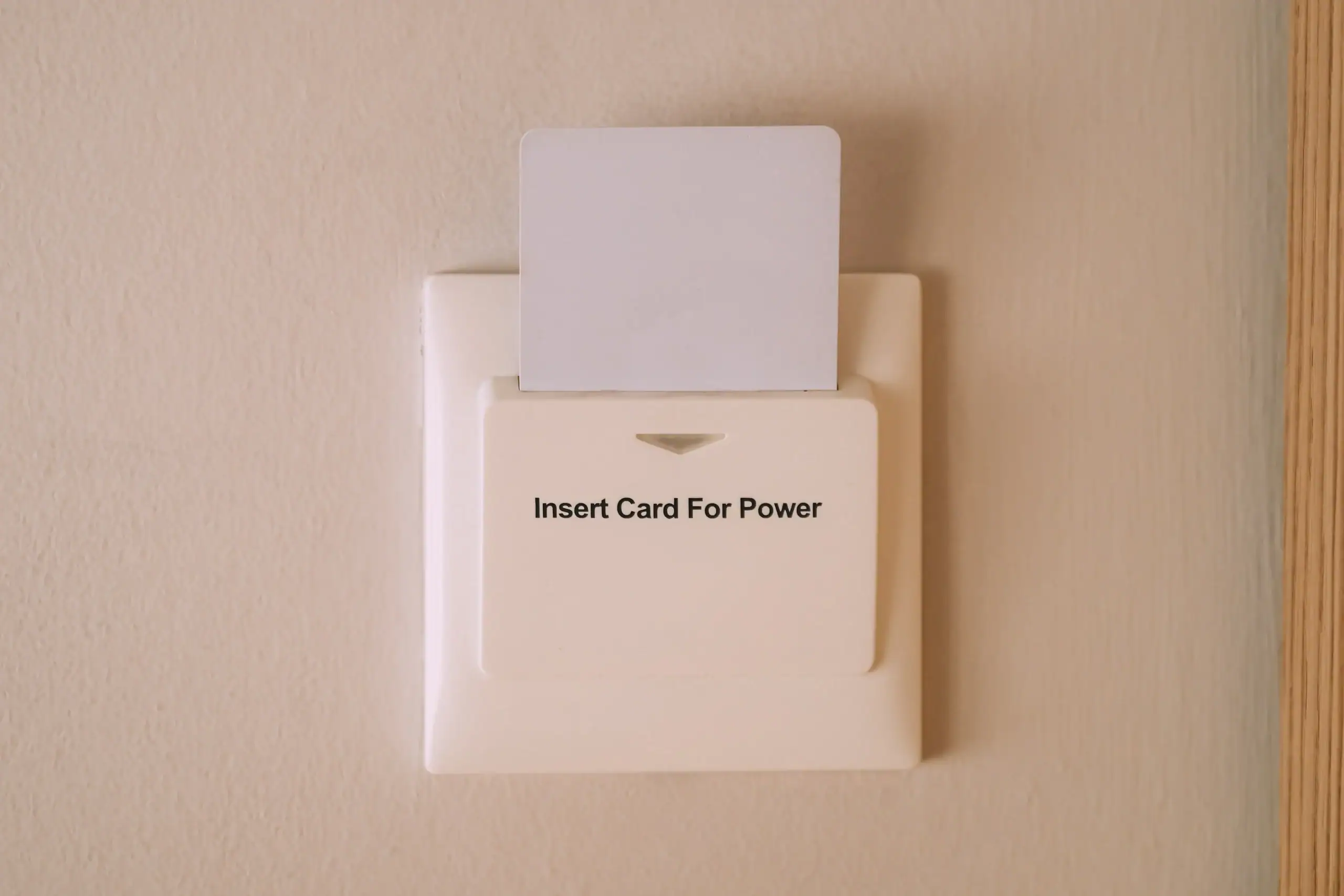
Installation happens on your timeline. We mount card readers or biometric scanners at entry points, wire controllers, configure your cloud-based management platform, and program initial credentials. You get hands-on training for the management software so you’re not calling us every time you need to add a new employee.
After we’re done, you’re controlling door access from your phone, tracking entry logs, and managing credentials without touching a physical key. And if something breaks or you need to expand the system, we’re 20-30 minutes away with parts already in the truck.

Ready to get started?
Mobile credentials mean your employees use their phones instead of cards they lose or forget. Biometric options add another security layer for high-sensitivity areas. Cloud-based management gives you real-time control from anywhere, not just a desktop in your office.
Integration matters in Concord, where 48% of organizations identified contactless solutions as a priority and 44% are actively implementing mobile access. Your system should connect with existing CCTV, alarm monitoring, and building management platforms without requiring a complete security overhaul.
You’re also getting audit trails that show exactly who accessed which doors and when. That’s critical for compliance in healthcare, professional services, and technical industries—the sectors that dominate Concord’s educated, high-income workforce. When you need to verify after-hours access or investigate a security incident, you have timestamped records, not guesswork.
Delaware County sees a crime every 40 minutes, with a rate of 21.89 incidents per 1,000 residents. Your access control system isn’t just convenience—it’s a documented security layer that reduces unauthorized entry, tracks movement, and gives you control when physical keys can’t.

Yes, and you should. Modern access control systems are built to integrate with CCTV and alarm monitoring so you’re managing security from one platform instead of juggling three different systems.
When someone badges in, your access control system can trigger cameras to record that entry point. If an unauthorized access attempt happens, it can alert your alarm monitoring service immediately. That integration means you’re not reviewing separate logs to piece together what happened—you see the badge attempt, the camera footage, and the alarm response in one timeline.
Most cloud-based access control platforms connect with major camera and alarm brands through APIs or direct integrations. If you’re already running Schlage, Medeco, or other commercial-grade systems, integration is usually straightforward. The key is working with installers who understand both access control and your existing infrastructure, so everything actually talks to each other instead of creating more headaches.
Depends on your system, but most commercial access control setups include offline functionality. Local controllers store credential data, so even if your internet connection drops, authorized users can still badge in and out.
What you lose during an outage is real-time monitoring and remote management. You won’t see live entry logs or be able to grant new credentials from your phone until connectivity returns. But employees with valid credentials can still access the building because the door controllers operate independently.
Once internet service restores, the system syncs all offline activity to your cloud platform. You’ll see every entry that happened during the outage, maintaining your complete audit trail. For businesses that can’t afford any access disruption, we can configure systems with cellular backup or redundant internet connections. That’s common in healthcare facilities, data centers, and other operations where 24/7 access is non-negotiable.
Immediately, from your phone or computer. That’s the whole point of modern access control—you’re not waiting for someone to show up with new keys or spending hours rekeying locks.
When you hire someone, you create their credential in the management platform, assign which doors they can access and during what hours, then send their mobile credential or program their access card. Takes about two minutes. When someone leaves, you deactivate their credential instantly, and they’re locked out across every door in your system.
Compare that to traditional locks where a terminated employee might have keys you don’t know about, or copies they made without permission. With access control, there’s no wondering—once you revoke their credential, they’re done. And if you need to adjust access levels, like giving a manager access to areas regular employees can’t enter, you’re changing permissions in software, not rekeying entire sections of your building.
Card readers use physical proximity cards or key fobs that employees scan at door entry points. They’re reliable and inexpensive, but people lose cards, forget them at home, or share them with unauthorized users.
Mobile credentials turn smartphones into access devices using Bluetooth or NFC technology. Employees unlock doors with their phones, which they’re far less likely to lose or forget. Mobile systems also let you issue and revoke credentials remotely without distributing physical cards. The downside is you need employees who consistently carry smartphones and keep them charged.
Biometric systems use fingerprints, facial recognition, or retina scans for access. Nobody can share, lose, or forget their fingerprint. Biometrics are ideal for high-security areas where you need absolute certainty about who’s entering. They’re more expensive and require more sophisticated hardware, so most businesses use biometrics selectively—server rooms, pharmaceutical storage, executive areas—while using cards or mobile credentials for general access.
Minimal maintenance, but there are ongoing costs you should know about upfront. Cloud-based systems typically charge monthly or annual subscription fees for the management platform, usually based on how many doors or users you’re managing.
Hardware maintenance is light. Card readers and door controllers are solid-state electronics without many moving parts. You might need to replace a reader every few years if it takes physical abuse, or swap batteries in wireless locks annually. Most issues come from doors and door hardware wearing out, not the access control electronics.
Software updates happen automatically with cloud-based systems, so you’re always running current security patches and features without IT involvement. If you’re running an on-premise system instead of cloud-based, you’ll need to handle updates manually and maintain your own server infrastructure.
The real cost savings come from not rekeying locks every time someone loses a key or leaves the company. One rekey event can cost several hundred dollars. Access control pays for itself quickly when you’re managing more than a handful of employees or dealing with any turnover.
Not if it’s done right. Most access control installations work with your existing doors and frames using the same prep holes as traditional locksets.
We mount card readers or biometric scanners on the wall next to the door, run low-voltage wiring to a controller (usually installed above the ceiling or in a nearby closet), and install electric strikes or magnetic locks that integrate with your current door hardware. For glass doors or locations where running wire through walls isn’t practical, wireless access control options eliminate most of the invasive work.
The exception is if your doors are old, damaged, or not compatible with electric locking hardware. In those cases, we’ll tell you upfront what needs upgrading. But for most commercial doors installed in the last 20 years, access control retrofits without major construction.
We’ve been doing this for four generations—we know how to install access control systems without destroying your doors, frames, or walls. We use the right tools, the right techniques, and we clean up after ourselves. You get functional security, not a construction zone.